Thousands of QNAP NAS devices have been infected with the QSnatch malware
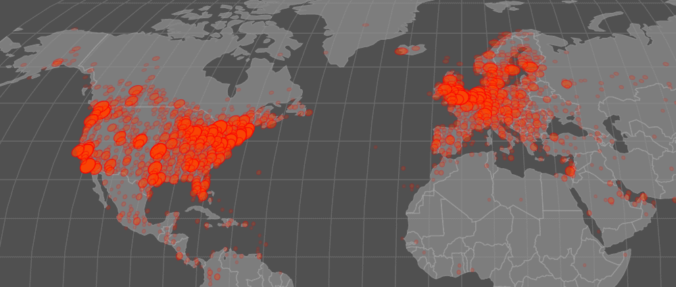
Hackers have infected thousands of network-attached storage (NAS) devices from Taiwanese vendor QNAP with a new strain of malware named QSnatch.
Over 7,000 infections have been reported in Germany alone, the German Computer Emergency Response Team (CERT-Bund) said today. Thousands more are believed to be infected worldwide, in what appears to be an ongoing outbreak.
Information on how QSnatch works is still scant, at the time of writing. The only report comes from the National Cyber Security Centre of Finland (NCSC-FI), the first cybersecurity organization to spot the malware last week.
NCSC-FI members have not yet discovered how this new threat spreads and infects QNAP NAS systems; however, once it gains access to a device, QSnatch burrows into the firmware to gain reboot persistence.
An analysis of the malware’s code revealed the following capabilities:
• Modify OS timed jobs and scripts (cronjob, init scripts)
• Prevent future firmware updates by overwriting update source URLs
• Prevents the native QNAP MalwareRemover App from running
• Extracts and steals usernames and passwords for all NAS users
These features describe the malware’s capabilities but don’t reveal its end-goal.