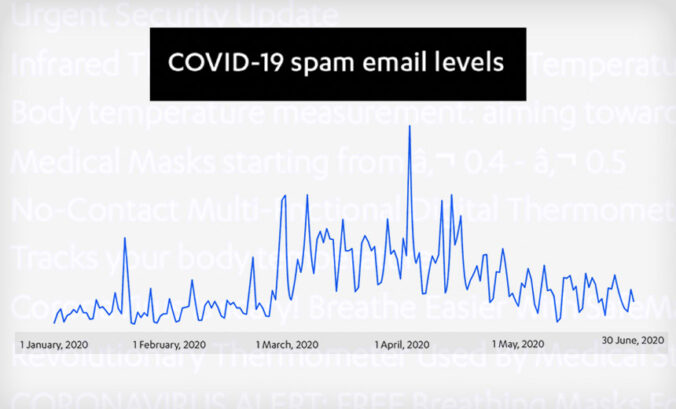
After reviewing online attack trends for the first half of the year, numerous cybersecurity firms agree: COVID-19 was king. As the pandemic has reshaped how many live and work, so too has it driven attackers to attempt to exploit work-at-home... Read More
Tag: social engineering
What does this mean for mobile phone users? It means that it’s even more important to stay vigilant about cybersecurity when using a mobile device. Here are some ways you can protect yourself, your data, and your phone. Lock your phone with a... Read More
Social engineering is the strongest method of attack against the enterprise’s weakest vulnerability, its people. Criminal hackers recognize this fact. In 2015, social engineering became the No. 1 method of attack, according to Proofpoint’s 2016... Read More
Cyberthreats to your business are usually blamed on outsiders—nefarious programmers writing malicious code designed to pilfer your corporate intelligence, siphon your confidential customer information and/or raid your financial data. Sometimes, the... Read More